2024.03.22
2026.03.11
What are the key points for success when conducting information security training through e-learning? We will also introduce how to choose materials.

In modern society, the importance of information security is increasing. For companies and organizations to avoid risks such as information leaks and cyber attacks, it is essential for each employee to correctly understand information security and take appropriate measures.
One way to meet these needs is by utilizing e-learning. However, it is necessary that learners can correctly understand the material and that the training is useful for actual work.
Therefore, this time, we will explain in detail the advantages and disadvantages of conducting information security training through e-learning, as well as key points for success when carrying out such training.
Table of Contents
1. What is Information Security Training through e-Learning?
2. Advantages of Information Security Training through e-Learning
3. Disadvantages of Information Security Training through e-Learning
4. Challenges and Solutions for Information Security Training through e-Learning
5. Examples of Content for Information Security Training through e-Learning
6. How to Choose e-Learning Materials for Information Security Training
7. Key Points for Creating Your Own e-Learning Materials for Information Security Training
8. Summary
1. What is information security training through e-learning?

First, let's grasp what information security training using e-learning is like.
What is information security training through e-learning?
Information security training through e-learning involves educating about the necessity of information security measures and basic knowledge via an online learning platform. There are various types of materials such as videos, simulations, quizzes, and tests. Ready-made materials are offered by various companies.
〈What is the training content?〉
The content of information security training covers a wide range of topics, including the Personal Information Protection Law, information security policies, and measures against internal fraud. Especially in training focused on cyberattacks, case studies based on actual incidents are incorporated, allowing learners to acquire more practical knowledge.
〈Courses Tailored to Each Role〉
Courses tailored to employees' positions and job responsibilities are sometimes available. For example, there may be courses focused on risk management for executives and courses specialized in advanced technical measures for system administrators. By considering the curriculum as needed, it helps to raise information security awareness throughout the entire organization.
2. Benefits of Information Security Training via e-Learning

Here, we explain the benefits of conducting information security training through e-learning.
〈Merit 1〉Learn at your own pace regardless of time or place
E-learning allows you to study without being restricted by time or location, as long as you have a device and an internet connection. Learners can progress at their own pace, making use of travel time and spare moments.
〈Merit.2〉You can review as many times as you need until you are satisfied
E-learning allows for repeated study. Even complex concepts and countermeasures that are difficult to memorize in one go can be thoroughly reviewed until fully understood.
〈Merit.3〉High learning effectiveness can be expected
E-learning can utilize interactive content and simulations, so high learning effectiveness can be expected. Furthermore, it also leads to acquiring practical information security knowledge.
〈Merit.4〉Easy to Reflect the Latest Information
Compared to paper-based materials such as books, e-learning makes it easier to update content. Therefore, the latest knowledge in the ever-changing field of information security and countermeasures against threats can be updated immediately.
〈Merit.5〉Provides low-cost and uniform education
As an advantage for administrators, e-learning is economical because, unlike group training, it can reduce costs such as printing materials, venue fees, and travel expenses for instructors and learners. Additionally, since the same content and materials are provided to all learners, it ensures uniform education.
In this way, e-learning can be said to be an effective and flexible method of learning for information security.
3. Disadvantages of Information Security Training via e-Learning
In the previous chapter, we explained the advantages of information security training through e-learning. While there are various benefits, there are also points to be cautious about during implementation and operation. Here, we will also touch on the disadvantages of e-learning and organize the points to consider when introducing it.
<Disadvantage.1> Learning devices are required
To learn through e-learning, devices such as computers, tablets, or smartphones are necessary. In companies where these devices are not sufficiently provided, additional costs may arise to establish a proper learning environment. Additionally, in locations without a stable internet connection, smooth learning may become difficult.
<Disadvantage.2> Difficult to maintain motivation because it is close to self-study
E-learning basically requires learners to progress at their own pace, demanding self-discipline. However, since there is no direct instruction or interaction with other learners as in face-to-face training, it can sometimes be difficult to maintain motivation.
<Disadvantage.3> Effort required for creating and customizing teaching materials
Preparing teaching materials is essential for introducing e-learning. While commercially available materials can be used, to include information tailored to your company's security policies and business content, it is necessary to create or customize the materials independently. Therefore, time and costs are incurred in creating the materials. Furthermore, since the field of information security is constantly evolving, regular updates to the materials are also required.
<Disadvantage.4> Lack of interaction with instructors can leave questions unresolved
In e-learning, opportunities for direct interaction with instructors are limited. Therefore, even if questions arise during learning, they may not be resolved immediately. This is especially true in specialized fields like information security, where it can be difficult to get answers to practical questions related to work, posing a risk of shallow understanding.
<Disadvantage.5> Difficult to provide learning tailored to each learner's individual case
Risks and countermeasures related to information security vary depending on job duties and positions. For example, the basic security measures for general employees differ from the advanced security measures for engineers in terms of what should be learned. However, e-learning often uses uniform materials, making it challenging to provide individualized support according to the learner's role.
There are also such disadvantages to information security training via e-learning. When implementing it, by improving the learning environment and devising mechanisms to maintain motivation, and combining face-to-face training or follow-up systems as needed, it is expected that the effectiveness of the training can be enhanced.
4. Challenges and Solutions of Information Security Training Using e-Learning
Information security training utilizing e-learning can be expected to provide effective learning, but there are also challenges. Below, we have summarized those challenges and their solutions.
In e-learning, learners need to maintain their own motivation for learning. However, if self-management skills are insufficient, there is a tendency for learning to not progress as planned, leading to a decrease in motivation.

By incorporating fun learning elements such as interactive content and gamification into educational materials, interest in learning increases, and motivation can be maintained.

Information security is a field that requires expertise, so some people struggle with the difficulty of creating e-learning materials.

It is also effective not to produce all the materials in-house, but to purchase existing content or request material production from vendors (sales companies) that provide e-learning materials. By enlisting the help of professionals with specialized knowledge, you can create high-quality materials.

In e-learning, unlike in group training sessions, it is difficult to have conversations or discussions with instructors and other participants, which can lead some individuals to feel isolated. As a result, there may be a decline in motivation and stagnation in learning.

By utilizing discussion forums and online chats, active interaction between learners and instructors will promote the resolution of questions and the sharing of information, leading to deeper learning.
By appropriately incorporating solutions to challenges in this way, the weaknesses of e-learning can be covered, leading to improved learning effectiveness and increased motivation.
5. Examples of Content in Information Security Training via E-learning

Although information security training via e-learning is a single term, in reality, there are various learning fields and a wide range of materials available. This chapter introduces an example of the learning content.
Personal Information Handling and Personal Information Protection Law
Learn appropriate methods and usage for handling personal information, as well as correct disposal methods. Furthermore, deepen your understanding of the overview, purpose, and scope of the Personal Information Protection Act.
Social Media Usage Rules and Risks
Understand the company's social media usage policy and learn the behavior guidelines based on it. Specifically, this includes precautions for information dissemination both internally and externally, appropriate responses to defamation and criticism, and protective measures against unauthorized access to social media accounts, among others.
Compliance
Understand the laws and regulations that companies must comply with, and learn about their importance and impact on society. Additionally, learn about the ethical standards and codes of conduct that companies uphold, and promote actions based on those principles.
Threats and Countermeasures of Targeted Attack Emails
Learn to understand the attack methods of targeted phishing emails, such as clever disguises, links, and attachments, and how to identify suspicious emails and respond appropriately. You will also understand the response and reporting procedures upon receipt, emphasizing the importance of quick initial response.
ID and Password Management
Learn how to safely and appropriately manage IDs and passwords through knowledge of creating hard-to-guess passwords, the importance of regular changes, and how to deal with social engineering attacks aimed at stealing passwords.
Risk of Using Cloud Services
Learn about the risks that may occur when using cloud services, such as data leaks and account hacks, and acquire the knowledge and skills to use them safely.
In training, it is also effective to cover case studies of incidents along with this kind of knowledge. By encountering real-life incident case studies, learners can feel the problems and risks more vividly, fostering a sense of urgency. As a result, their understanding of information security deepens, leading to the acquisition of appropriate countermeasures and preventive measures.
6. How to Choose e-Learning Materials for Information Security Training
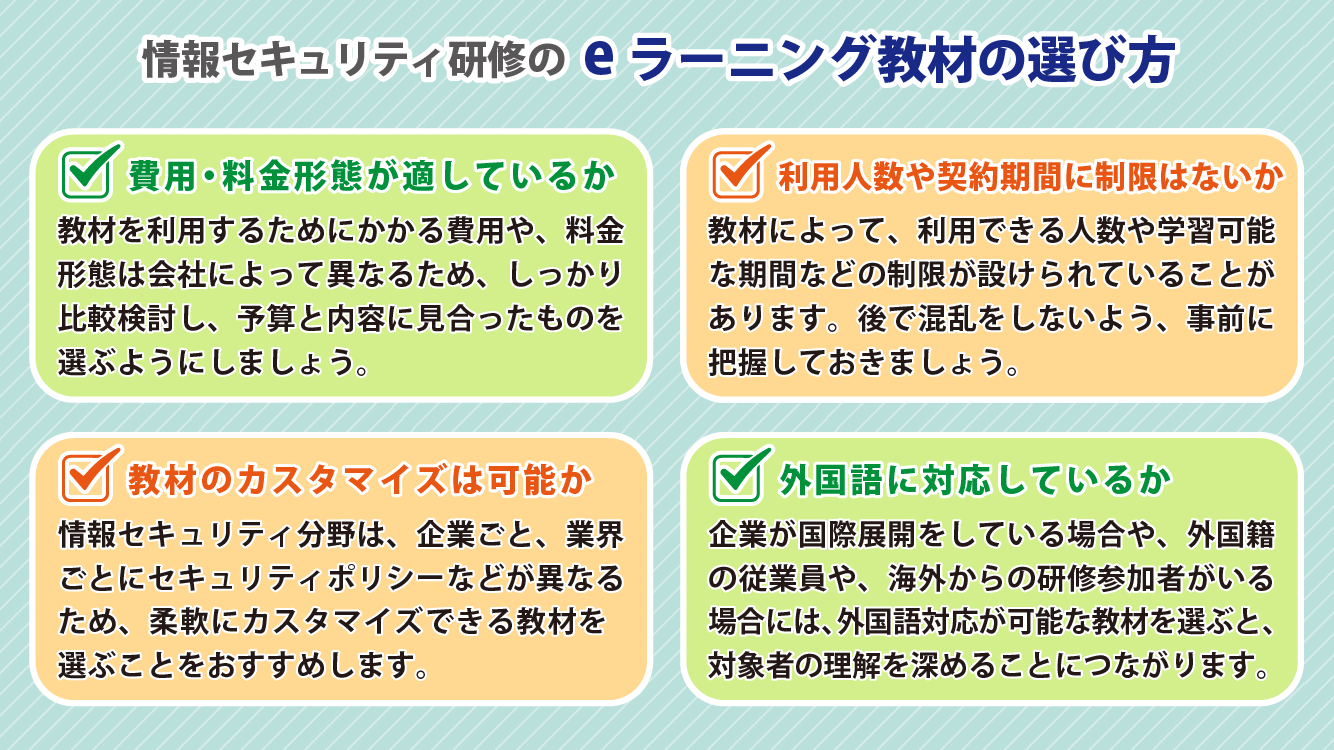
Choosing the right materials is also important for successfully conducting information security training using e-learning. Here are some key points to keep in mind when selecting materials.
Is the cost and pricing structure appropriate?
The cost to use the teaching materials varies depending on the company providing them. Additionally, pricing structures differ widely, ranging from free options, one-time purchase with only an initial fee, subscription models with monthly fees, to pay-per-use charges each time the materials are accessed. When implementing, be sure to compare each material and select one that fits your budget and content requirements.
Are there any restrictions on the number of users or the contract period?
Some materials may have restrictions on the number of users and the duration of study. By understanding the number of participants and the usage period in advance, you can prevent confusion and avoid unnecessary expenses.
Can the teaching materials be customized?
Teaching materials are divided into those that are used as provided by the supplying company and those that are customized for use within the company. In the field of information security, since security policies and required know-how differ by company and industry, it is recommended to choose materials that can be flexibly customized.
Is it compatible with foreign languages?
When a company is expanding internationally or has foreign employees or training participants from abroad, it is important to choose materials that are available in foreign languages. Learning in one's native language can deepen understanding and improve learning effectiveness.
We recommend selecting materials that match the training objectives and the needs of the participants while considering these points.
7. Key Points for Creating Your Own e-Learning Materials for Information Security Training

To conduct effective information security training through e-learning, it is important that the content of the materials is practical for the learners. This chapter introduces three key points to keep in mind when creating training materials.
〈Point.1〉Consider customizing rather than creating from scratch
Creating materials from scratch requires time and cost. Therefore, customizing commercially available materials or existing content is also an option. In particular, by incorporating security risks that learners face and actual case studies, you can make the content more practical and relatable, tailored to your company's operations.
〈Point.2〉Reflect the Latest Internal Information in the Training Materials
Information security risks change daily, and accordingly, the content of the training materials requires continuous updates. Especially by incorporating the latest incident cases and internal security policies, the content becomes more realistic for learners, enhancing learning effectiveness and making it easier to capture learners' interest and attention.
〈Point.3〉Seek advice from experts
When creating materials, it is also effective to seek advice from information security experts. By incorporating expert opinions, you can create content that is accurate and practical. Additionally, having the materials supervised or reviewed by experts helps enhance their reliability.
By keeping these points in mind, let’s aim to realize more effective and practical information security training.
8. Summary

To deepen the understanding of the constantly changing field of information security, it is essential to have up-to-date materials that reflect the latest information and a flexible learning environment. E-learning equipped with these elements can be considered the optimal learning tool.
To maximize the learning effectiveness of such e-learning, the "quality of the materials" is crucial.
As explained in this blog, there are various types and ways to use learning materials. Since some materials offer free trials, actively utilize them and carefully select by assessing ease of use, cost performance, and whether they meet your company's needs.
Human Science also offers a wide range of educational materials related to information security.
These include materials focused on devices such as personal computers and smartphones, as well as those specialized for telework and remote work. Each covers essential knowledge by theme and incorporates interactive elements such as quizzes.
We also offer a free trial, so if you are considering it, please feel free to try it out.
Please refer to Human Science Co., Ltd.'s e-learning site.